April 15, 2026

How one stolen mailbox gave an attacker access to sensitive financial documents, launched a phishing wave across related organizations, and showed why today’s BEC attacks are harder to catch in real time.
Business email compromise is no longer just a fake invoice or a suspicious email from overseas. Today’s attacks are quieter, more targeted, and much more convincing.
In this case, our team investigated an incident that started with a single compromised employee mailbox and quickly expanded into a broader phishing campaign that touched multiple related organizations. The confirmed compromise was limited to one mailbox, but the attack shows how much damage can begin with just one successful login.
The attacker didn’t smash in. They blended in.
One of the reasons business email compromise remains so effective is that attackers no longer have to behave like obvious outsiders.
In this case, the initial compromise appears to have started with stolen email credentials, most likely obtained through a phishing-style login theft or a similar credential capture method. Once the attacker had access, they logged in using infrastructure designed to look ordinary rather than suspicious.
That matters because modern attackers can hide behind proxy services and internet connections that make their traffic appear local, familiar, or tied to legitimate providers. Instead of showing up as an obviously foreign or high-risk login, the activity can look like it came from the same general area as the victim’s office. That makes real-time detection much harder, especially for organizations that still rely heavily on location-based alerts or simple IP reputation checks.
In plain terms: the login may not have looked bad enough at first glance, even though it was the beginning of a serious incident.
Once inside, the attacker studied the business
After gaining access to the mailbox, the attacker did not immediately begin sending obvious spam.
Instead, they spent time reviewing financially sensitive email threads and attachments tied to active real estate transactions. The mailbox activity showed clear interest in documents related to:
- due diligence deposits
- check copies
- attorney communications
- payment and closing records
The mailbox became a launch point
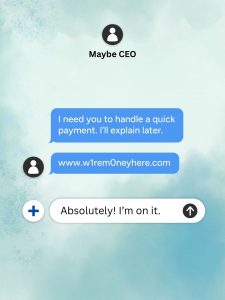
After reviewing sensitive financial content, the attacker used the compromised mailbox to send a phishing message to a large number of internal and external recipients.
That second stage changed the incident from a single-account compromise into a multi-organization exposure event.
Recipients across related organizations opened the message, clicked the embedded link, and in some cases were followed by suspicious sign-in attempts or blocked account-setting activity shortly afterward. Not every exposed user was confirmed compromised, but the pattern showed how quickly one trusted mailbox can become a weapon.
That is one of the most important lessons in this case: a compromised mailbox is not only a data exposure issue. It can also become a highly effective delivery platform for follow-on phishing because the message comes from a real account, inside a real business relationship, with real trust behind it.
Why this type of BEC is so dangerous
Traditional email security often focuses on obvious warning signs:
- strange sender domains
- known malicious IP addresses
- unexpected geographies
- clearly fraudulent wording
- compromised real accounts
- real email conversations
- real attachments
- local-looking or residential-style internet traffic
- patient reconnaissance before acting
What was confirmed in this case
Based on the reviewed logs, one employee mailbox was conclusively confirmed compromised.
The evidence showed that the attacker:
- authenticated into the mailbox without authorization
- reviewed financially sensitive email threads
- accessed and downloaded related attachments
- used the mailbox to send a broad phishing wave to internal and external recipients
The bigger lesson for real estate, title, and financial operations
For organizations that handle transactions, escrow activity, closings, legal documents, or payment instructions, this case is a reminder that email remains one of the most valuable attack surfaces in the business.
When attackers gain access to a mailbox tied to money movement, they do not need to guess. They can learn directly from the inbox:
- which deals are active
- which parties are involved
- what documents are exchanged
- how requests are normally phrased
- when a last-minute change might seem believable
Final takeaway
This incident began with one stolen mailbox, but the real danger came from what the attacker did after getting in. They studied financial records, learned the rhythm of the business, and used a trusted account to widen the attack.
The confirmed compromise may have started with a single user, but the exposure did not stay there.
Modern business email compromise is built to look normal. That is exactly what makes it so effective.
Think a mailbox in your organization may have been compromised? We help organizations investigate suspicious mailbox activity, confirm the scope of exposure, identify follow-on phishing risk, and contain business email compromise. Book a 15 Minute Discovery Call to learn more.