March 25, 2026

Operation Winter SHIELD for Raleigh Law Firms: The FBI’s 10 Actions to Improve Cyber Resiliency
If you run a law firm in Raleigh (or anywhere in North Carolina), your technology is part of your practice—email, document management, e-signatures, billing, remote access, client portals, and the vendors that support them. Operation Winter SHIELD is a concise framework from the FBI that distills “the 10 most impactful actions organizations can take to improve resilience against cyber intrusions.”
If you’re like most of us, the headlines of major companies getting breached may cause us to have a knee-jerk reaction when it comes to IT and cybersecurity. While it makes sense to have a healthy level of awareness, feelings of fear alone rarely lead to increasing the maturity posture of your firm. This is where Operation Winter SHIELD comes in strong for your law firm: the FBI has recommended ten actionable steps that EVERYONE can take RIGHT NOW to decrease cyber risk and grow cybersecurity operational maturity.
What is Operation Winter SHIELD?
Operation Winter SHIELD is the FBI’s effort to focus organizations on the most effective improvements they can make to reduce cyber risk. The FBI notes these recommendations were developed with domestic and international partners and draw on recent investigations to reflect how adversaries behave and where defenders commonly have gaps.
For a law firm, the value is simple: it’s a prioritized list you can operationalize without needing to guess which controls matter most.
The FBI’s 10 Actions translated for Raleigh law firms
1) Adopt phish-resistant authentication
Why it matters: The FBI highlights that many breaches begin with stolen passwords, and phish-resistant methods make access significantly harder for attackers.
What “start now” looks like in a law firm:
- Prioritize high-impact accounts (partners, firm administrators, finance, IT admin roles).
- Use phish-resistant options such as FIDO2 security keys or device-bound passkeys for authentication, remote access, and critical systems.
- If you use authenticator apps, require number-matching and domain display; avoid push-only approvals.
- Eliminate SMS-based MFA and disable legacy authentication methods.
2) Implement a risk-based vulnerability management program
Why it matters: The FBI notes adversaries often exploit known vulnerabilities that remain unaddressed when there’s no ownership, no mitigation process, and unclear deadlines.
What “start now” looks like:
- Maintain a complete asset inventory with owners and business criticality.
- Set remediation timelines based on risk (critical systems measured in days, not months).
- Use authenticated internal scans to reflect actual configurations.
- Document exceptions with compensating controls and fixed completion dates.
3) Track and retire end-of-life technology on a defined schedule
Why it matters: End-of-life systems don’t receive security updates and are routinely targeted.
What “start now” looks like:
- Maintain a rolling 12-month end-of-life forecast reviewed quarterly with owners and procurement.
- Track end-of-life systems by product, owner, location, and retirement date.
- Replace or isolate end-of-life assets; if delays occur, apply compensating controls with firm decommission dates.
4) Manage third-party risk
Why it matters: The FBI warns your security extends only as far as your least-protected vendor with network or data access, and adversaries exploit these gaps to bypass stronger defenses.
What “start now” looks like:
- Keep one list of third parties with access/data-handling responsibilities and named owners.
- Require strong authentication, least-privilege access, and monitored gateways where feasible.
- Audit for and disable unused accounts.
- Contractually require rapid breach notification, encryption, and annual control verification.
- Revoke access and confirm data disposition when contracts change or end.
5) Protect security logs and preserve them for an appropriate time
Why it matters: Reliable, preserved logs are essential for detection, response, and attribution and adversaries often try to erase them.
What “start now” looks like:
- Centralize key logs (authentication, email, endpoint, network, DNS, remote access, cloud audit logs) into a SIEM or centralized platform, and export daily to protected, immutable storage.
- Retain logs based on legal and response needs (12 months is a common baseline).
- Synchronize system clocks and validate retention.
- Quarterly, review logs for activity tied to a single user/server to find gaps.
6) Maintain offline, immutable backups and test restoration
Why it matters: The FBI notes backups are routinely targeted early in intrusions, and resilience depends on isolation and tested recovery.
What “start now” looks like:
- Follow the 3-2-1 backup rule (three copies, two media types, one stored offline and immutable).
- Secure backup platforms with strong authentication, separate admin accounts, and consoles limited to secured devices.
- Define recovery requirements, including configurations and identity systems.
- Test restorations regularly, measure recovery time, and remediate gaps.
7) Identify, inventory, and protect internet-facing systems and services
Why it matters: Unnecessary exposure creates low-effort entry points for attackers.
What “start now” looks like:
- Maintain a concise list of internet-reachable systems with owners.
- Remove unnecessary exposure; require authenticated gateways for what remains.
- Disable direct internet-facing remote desktop; use brokered access instead.
- Regularly scan public IP space to detect new exposures.
8) Strengthen email authentication and malicious content protections
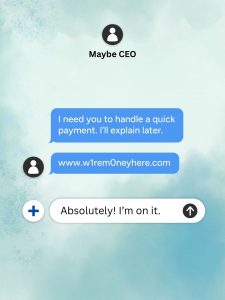
Why it matters: The FBI states email remains a favored initial access vector for intrusions and fraud.
What “start now” looks like:
- Publish and enforce DMARC, SPF, and DKIM for all sending domains; align third-party senders.
- Progress DMARC from monitoring to quarantine to reject as alignment matures.
- Quarantine high-risk attachments, block internet-sourced macros, and sandbox suspicious files.
- Enable time-of-click link protection and restrict automatic external forwarding.
9) Reduce administrator privileges
Why it matters: Broad, persistent administrative access enables rapid escalation if credentials are compromised.
What “start now” looks like:
- Minimize admin accounts and admin group memberships.
- Use admin privileges only when necessary; use standard accounts otherwise.
- Require just-in-time admin access from secured devices using separate admin accounts.
- Restrict where admin logins can occur and block use on standard workstations.
- Monitor/alert on privilege changes and new admin accounts.
- Remove local admin rights from user devices; approve exceptions with expiration dates.
10) Exercise your incident response plan with stakeholders
Why it matters: Practiced organizations respond faster, contain more effectively, and reduce impact.
What “start now” looks like:
- Maintain a concise incident response playbook: roles, decision authority, isolation actions, evidence preservation.
- Run a focused 60-minute tabletop exercise quarterly with technical, legal, communications, operations, and leadership.
- Include law enforcement contacts in the plan (such as your local FBI field office) for rapid coordination.
A simple cybersecurity maturity roadmap for a Raleigh law firm
If you’re wondering “where do we start without boiling the ocean?”, a practical sequence is:
First 30 days: phish-resistant authentication for high-impact accounts; lock down email protections; remove obvious internet exposure; start a real asset inventory.
Next 60 days: vulnerability management with deadlines; EOL tracking; backup hardening + restore testing; admin privilege reduction.
Next 90 days: centralized logs with retention; third-party access reviews; quarterly tabletop cadence with documented outcomes.
This sequencing aligns with the FBI’s emphasis on credentials, patching, exposure reduction, recovery, and practiced response.
How an MSP helps Raleigh law firms operationalize Winter SHIELD
Operation Winter SHIELD is not just a checklist it’s an operating model. A strong MSP helps you:
- Turn “start now” items into owned processes (who does what, how often, and what success looks like).
- Implement controls with minimal disruption (especially authentication, email policy changes, and admin privilege boundaries).
- Measure maturity over time using recurring scans, log coverage reviews, restore tests, and quarterly exercises.
- Coordinate vendors so third-party access and breach notification expectations are documented and enforced.
For managing partners, that means visibility and reduced business risk. For office managers, it means repeatable operations. For technical paralegals, it means fewer fire drills, and better tools to keep the firm running.
Next step: use Winter SHIELD as your firm’s 2026 cyber baseline
Operation Winter SHIELD gives law firms a practical, FBI-backed starting point: protect identity, patch what matters, reduce exposure, preserve the evidence you’ll need, back up safely, and practice your response.
If your Raleigh law firm wants to increase cybersecurity maturity with these 10 actions as the baseline, an MSP can help you assess gaps, prioritize work, implement controls, and keep them operating month after month so cybersecurity supports the practice instead of interrupting it.
Interested in learning how your current setup compares to these basic cybersecurity benchmarks? Our specialists are available for a free, 15-minute call to learn more about your firm. Schedule an appointment here.
Link to Operation Winter Shield: https://www.fbi.gov/investigate/cyber/ten-actions-to-improve-cyber-resiliency Resiliency — FBI